As a total sucker for anything skimming-related, I was interested to hear from a reader working security for a retail chain in the United States who recently found Bluetooth-enabled skimming devices placed over top of payment card terminals at several stores. Interestingly, these skimmers interfered with the terminal’s ability to read chip-based cards, forcing customers to swipe the stripe instead.

The payment card skimmer overlay transmitted stolen data via Bluetooth, physically blocked chip-based transactions, and included a PIN pad overlay.
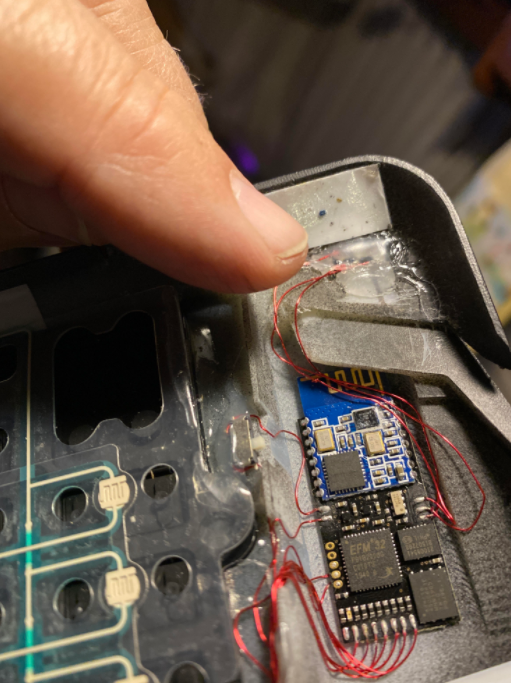
Here’s a closer look at the electronic gear jammed into these overlay skimmers. It includes a hidden PIN pad overlay that captures, stores and transmits via Bluetooth data from cards swiped through the machine, as well as PINs entered on the device:

The hidden magnetic stripe reader is in the bottom left, just below the Bluetooth circuit board. A PIN pad overlay (center) intercepts any PINs entered by customers; the cell phone battery (right) powers all of the components.
My reader source shared these images on condition that the retailer in question not be named. But it’s worth pointing out these devices can be installed on virtually any customer-facing payment terminal in the blink of eye.
Newer, chip-based payment cards are more costly and difficult for thieves to clone, but virtually all cards still store card data on a magnetic stripe on the back of the cards — mainly for reasons of backwards compatibility. This overlay skimmer included a physical component designed to block the payment terminal from reading the chip, forcing the customer to swipe the stripe instead of dip the chip.
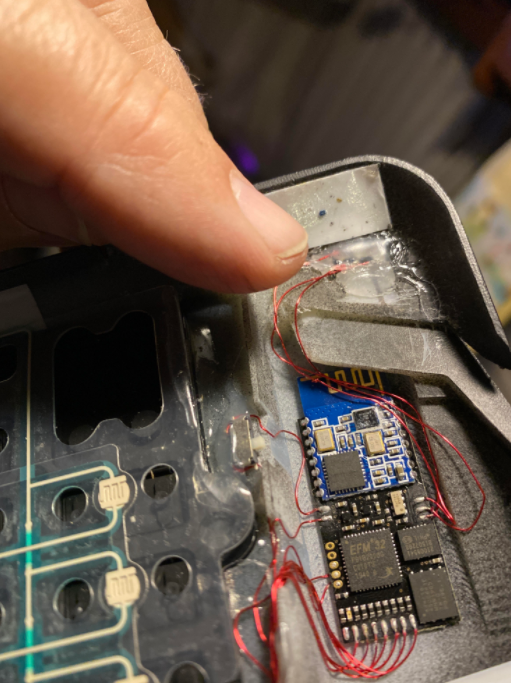
The magnetic stripe reader (top right) worked with a component designed to block the use of chip-based payment cards.
What’s remarkable is that these badboys went undetected for several weeks, particularly given that customers would have been forced to swipe.
“In this COVID19 world, with counter and terminal wipedowns frequent it was surprising that nobody noticed the overlay placements for a number of weeks,” the source said.
I realize a great many people use debit cards for everyday purchases, but I’ve never been interested in assuming the added risk and pay for everything with cash or a credit card. Armed with your PIN and debit card data, thieves can clone the card and pull money out of your account at an ATM. Having your checking account emptied of cash while your bank sorts out the situation can be a huge hassle and create secondary problems (bounced checks, for instance).
Want to learn more about overlay skimmers? Check out these other posts:
How to Spot Ingenico Self-Checkout Skimmers
Self-Checkout Skimmers Go Bluetooth
More on Bluetooth Ingenico Overlay Skimmers
Safeway Self-Checkout Skimmers Up Close
Skimmers Found at Wal-Mart: A Closer Look
Read More
The post Bluetooth Overlay Skimmer That Blocks Chip appeared first on Malware Devil.
https://malwaredevil.com/2021/02/15/bluetooth-overlay-skimmer-that-blocks-chip-2/?utm_source=rss&utm_medium=rss&utm_campaign=bluetooth-overlay-skimmer-that-blocks-chip-2