 A peek at open XDR technology, and defense that held up better than the Kansas City Chiefs.
A peek at open XDR technology, and defense that held up better than the Kansas City Chiefs.
(image by detakstudio, via Adobe Stock)
Protecting the Super Bowl from cyberattackers is no small task. In fact, it’s a sprawling, messy mass of challenges converging on a day when (almost) 100 million people are watching.
This year, much of the job fell to ReliaQuest, the official cybersecurity partner for both the Tampa Bay Buccaneers and the NFL Super Bowl LV Host Committee. ReliaQuest CEO Brian Murphy and CTO Joe Partlow lay out the tasks:
Protecting the stadium’s wireless access points and payment systems. Defending the scoreboard from vandalism and sad fans hoping to change the score. Locking down the volunteer staff’s background checks and COVID screening info. Securing coaches’ tablets and comms so their playbooks and play-calling are kept confidential. Making sure injury reports, starting lineups, and other valuable data aren’t leaked to the competition and the gambling public early. The list goes on. It means monitoring threat intelligence reports, scraping social media, shifting defense to respond to shifting threats.
(And, hopefully, doing so as effectively as the Buccaneers’ defense was against the Kansas City Chiefs’ attacks in the Bucs’ 31-9 victory that night.)
It would be a big undertaking in any year, for sure, but in 2021 the pandemic created new challenges, Murphy and Partlow explain.
Attendance in the stadium at Super Bowl LX was slashed from 62,000 to 22,000, but the bigger change affecting infosec was in the viewership outside of the stadium.
“‘Watch parties weren’t happening,” Murphy explains.
Usually, he says, people gather to watch the game, at restaurants, bars, and friends’ houses with big-screen TVs. This year, instead, people were watching alone, at home, on a variety of devices.
The result: Although the overall viewership ratings were the lowest for a Super Bowl since 2006, live-streaming viewership rocketed up by 65%, according to CBS.
Expecting the bump in online viewers, ReliaQuest also expected an accompanying bump in overall security events leading up to and during the game. The company hypothesized that its overall customer base might experience more attacks during the 2021 Super Bowl than in 2020.
They were right: In fact, ReliaQuest detected a 20.2% increase in total security events, year over year. There were upticks in phishing and ransomware attacks. The most noteworthy change was the increase in malicious streaming services, luring victims with promises like, “Watch the Super Bowl for free! Just download here.”
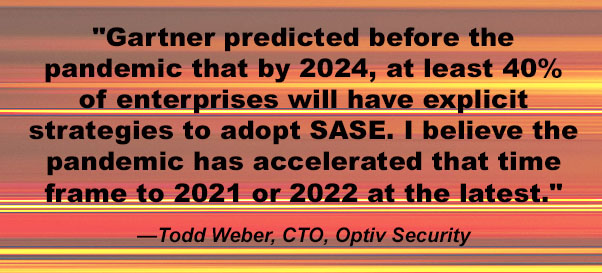
Defending against the wide variety of threats related to the event requires an array of intelligence, detection, and response tools – security information and event management (SIEM), endpoint detection and response (EDR), and threat intelligence, for starters, and in in this case, pulled together by an extended detection and response product (XDR). Partlow and Murphy explain that their company’s XDR offering is an “open XDR” technology. By “open,” they mean the XDR is vendor-agnostic. It integrates security tools from a variety of security companies – some Carbon Black here, some Tenable there, etc.
This approach can also, for example, simplify a merger or acquisition, Partlow explains.
“Each company probably chose their security tools for a good reason,” he says, “As that [merged] enterprise, I don’t have to rip-and-replace and make it all one logo.”
Although bruised-up Chiefs quarterback Patrick Mahomes might disagree, attacks on Super Bowl Sunday were handled without major incident – “aside from the streaker,” says Partlow. But that, he notes,”was a physical security breakdown.”
Sara Peters is Senior Editor at Dark Reading and formerly the editor-in-chief of Enterprise Efficiency. Prior that she was senior editor for the Computer Security Institute, writing and speaking about virtualization, identity management, cybersecurity law, and a myriad … View Full Bio
Recommended Reading:
Comment |
Email This |
Print |
RSS
More Insights
The post Securing Super Bowl LV appeared first on Malware Devil.
https://malwaredevil.com/2021/02/26/securing-super-bowl-lv-2/?utm_source=rss&utm_medium=rss&utm_campaign=securing-super-bowl-lv-2
















Be the first to post a comment regarding this story.