How To

Lots of people use Gmail for their email, either using Google’s website in a web browser, or through an email client. You may use an @gmail address, or you may have a domain hosted on Google’s G Suite. When you use Google for your email—as well as for search, maps, and more—there are a number of security and privacy options you can set.
Google has a full set of tools you can use to check and tweak your security settings, for both Gmail and for the rest of its services. In this article, you will discover how to run a Google Security Checkup, a Privacy Checkup, and how to tweak Google’s settings, so your account is secure.
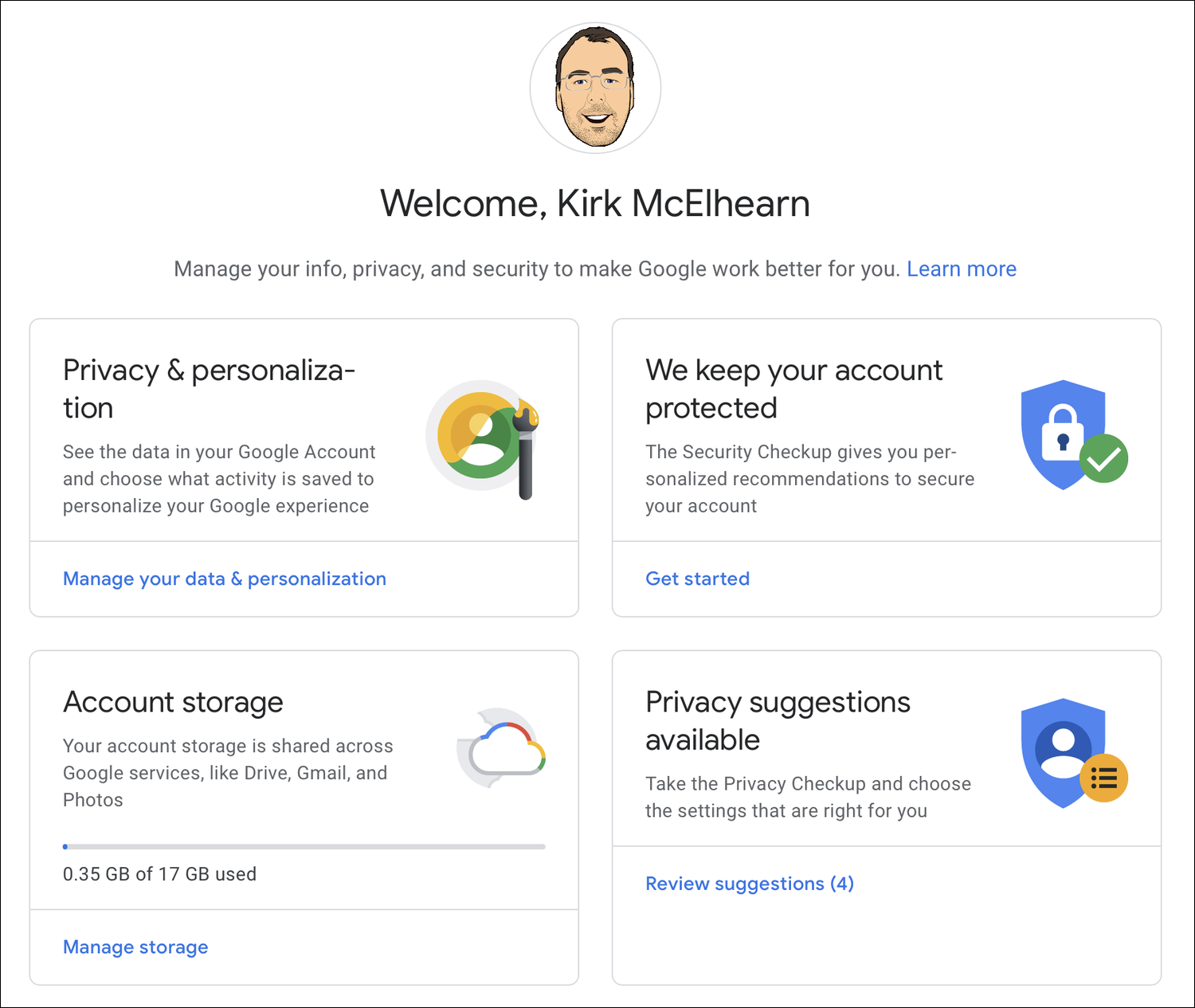
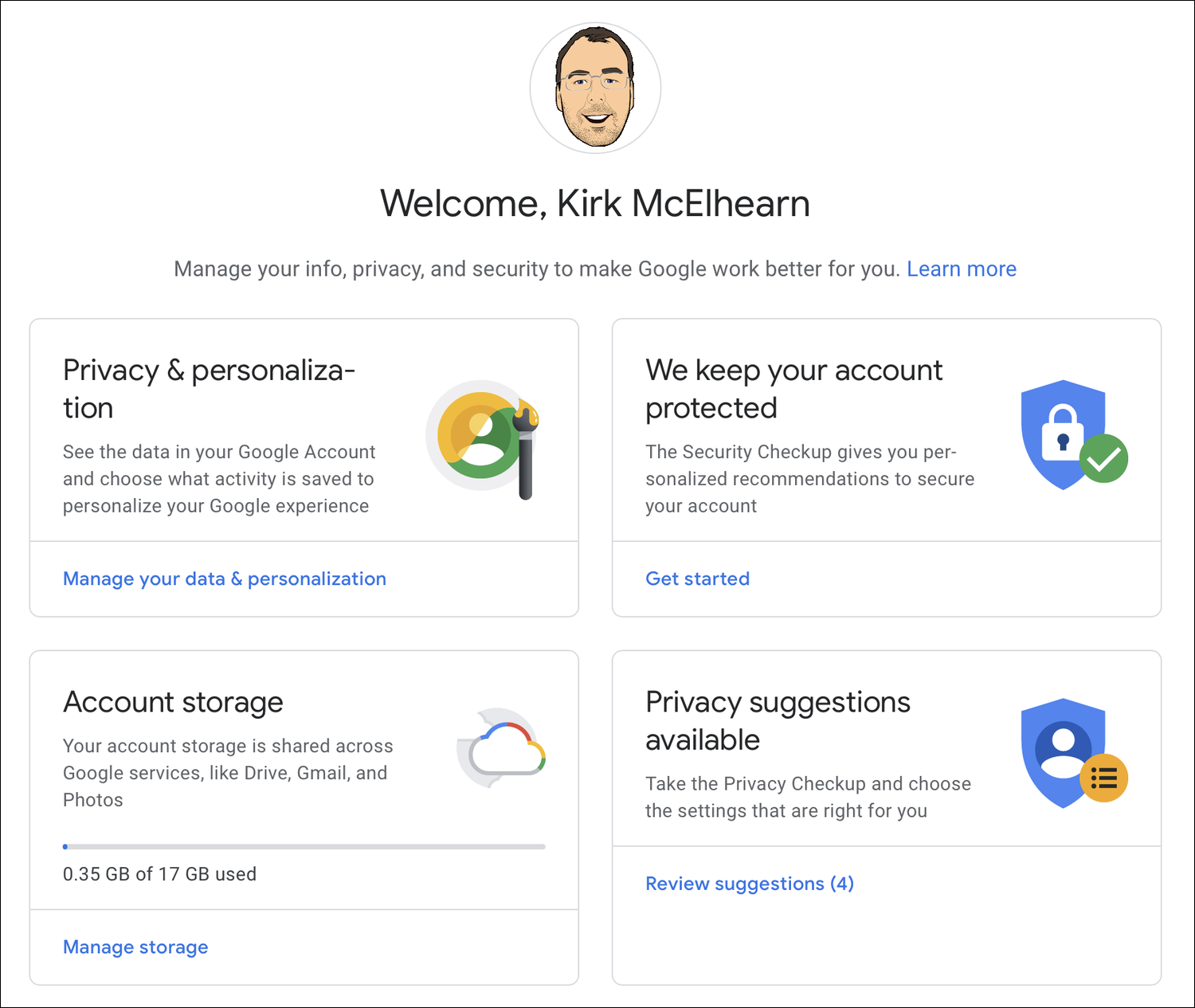
Begin by going to myaccount.google.com, where you can manage many of the settings for your Google account. You’ll see several sections on this page, one for Privacy & Personalization, one for Security Checkup (We keep your account protected), one for Account storage, and one that offers to let you Take the Privacy Check-up (Privacy suggestions available). And there are additional options in the sidebar, such as your Personal Info, Data & Personalization, Security, People & Sharing, and Payments & Subscriptions.
Google Security Checkup
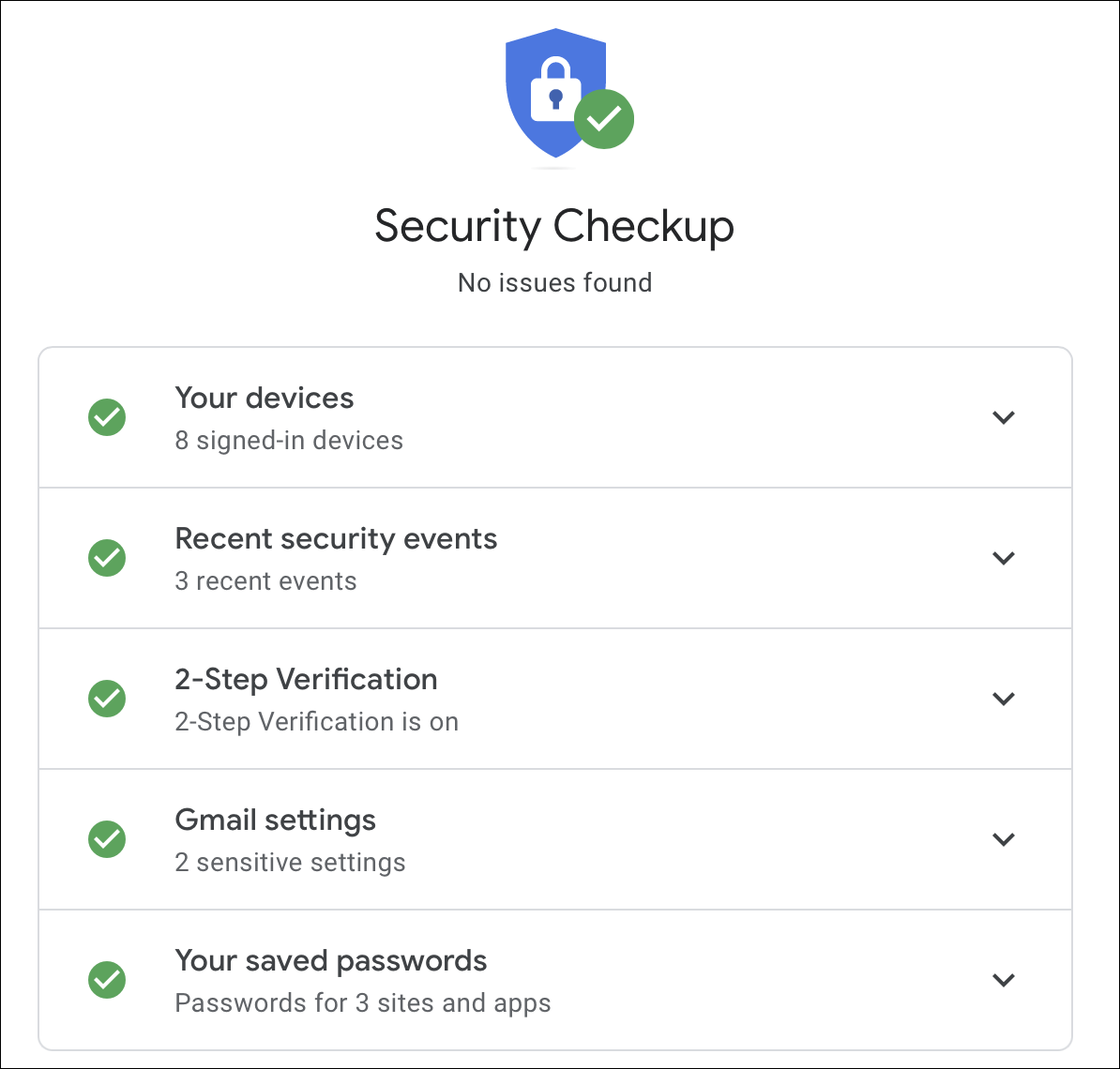
Start with the Security Checkup, in the We keep your account protected section (this may display Security issues found, if there are issues you need to check). Click Get Started in that section, sign into your account, and follow the instructions. There are five items in this checklist to run through.
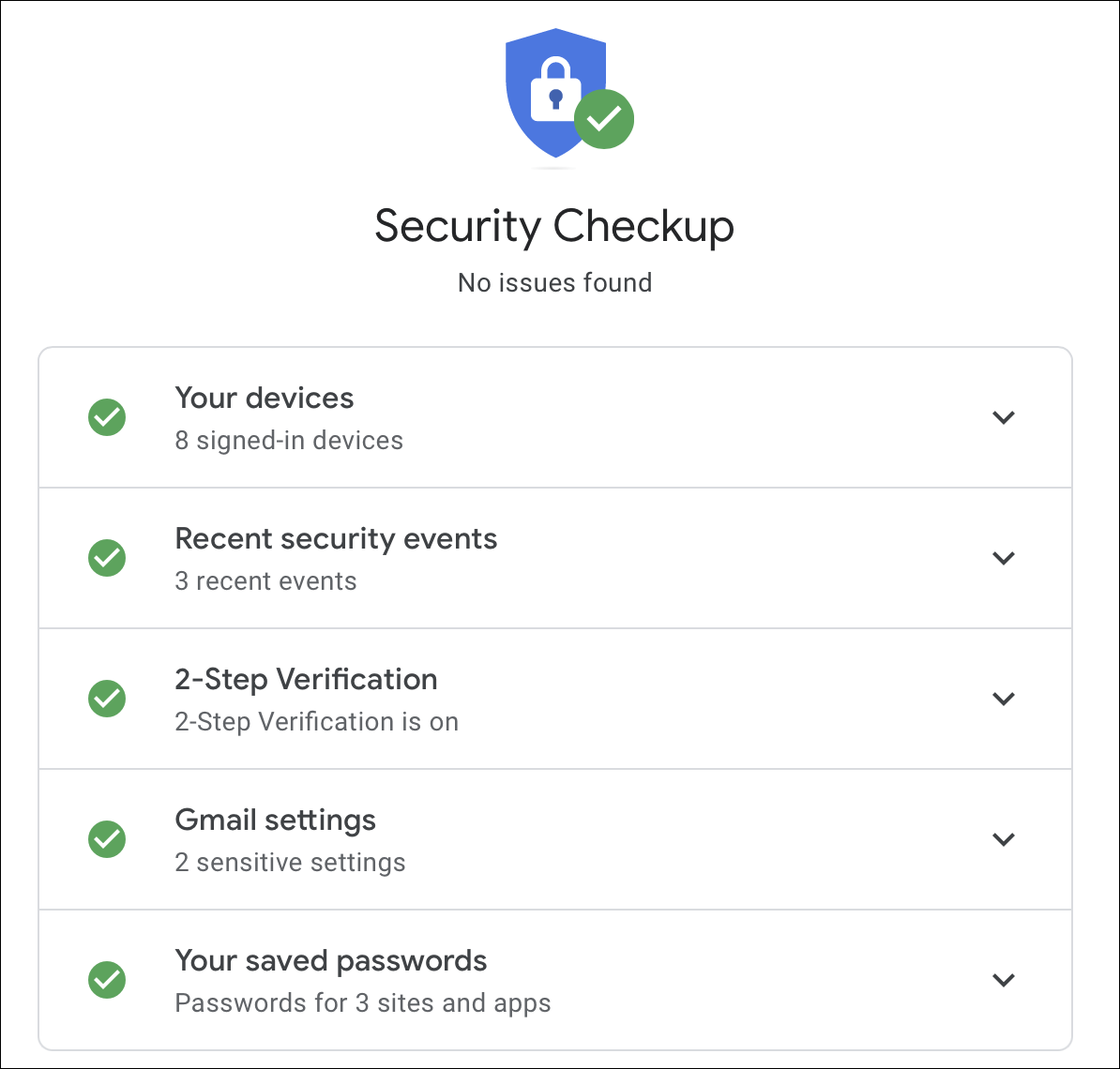
Your devices
You can check all your signed-in devices. These are computers, tablets, and smartphones that have logged into your Google account. If you’ve recently sold or given away a device, it’s a good idea to remove it from the list. Or if you see an unfamiliar device in the list, you should remove it. Click the three-dot menu and choose Sign Out. If you need more information, click Don’t recognize a device? and follow the instructions.
Recent security events
You can now see recent security events. This tells you when you logged into your account from different devices, and lists any changes you’ve made, such as to your password, or to your recovery phone number or email address. If anything looks suspicious, click Don’t recognize an event? and follow the instructions.
2-Step Verification
The next section is for 2-Step Verification. We’ve discussed two-step verification for a number of services, such as Amazon and iCloud. Google offers a similar feature, which protects your email and the rest of your Google account. It’s a good idea to set it up if you haven’t already. If you have already set up 2-Step Verification, you’ll see your phone numbers here, and you’ll also see if you have set up an authenticator app to create one-time codes. If not, you can turn on 2-Step Verification. (See this Google page for instructions on how to turn this on.) We’ve also looked at using a hardware security key to add extra protection to your account; Google has settings for this, which we explain in this article.
Gmail settings
In the Gmail settings section, you’ll see addresses that you have blocked, and you may see information about the fact that your name shows on your emails (rather than just the @gmail address), if you have automatic forwarding on, or other features. But most of the settings for your Gmail account are accessible from within the account. See below for more on Gmail settings.
If you return to the main account page, you can access other settings in the sidebar.
Your saved passwords
This section tells you how many passwords you’ve saved, for sites and apps, and offers to do a Password Checkup. This latter feature is useful to see if you’ve been reusing passwords, or if any of your passwords are weak.
Personal info
This section is where you update information about yourself, such as your name, date of birth, and password; this is information that is visible to others in your Google profile. (Edit what is visible in the Choose what others see section at the bottom of the page.) You can edit your contact info – alternate email addresses, a recovery email address, and others. You can also edit and verify a phone number that you use for two-factor authentication.
Data & personalization
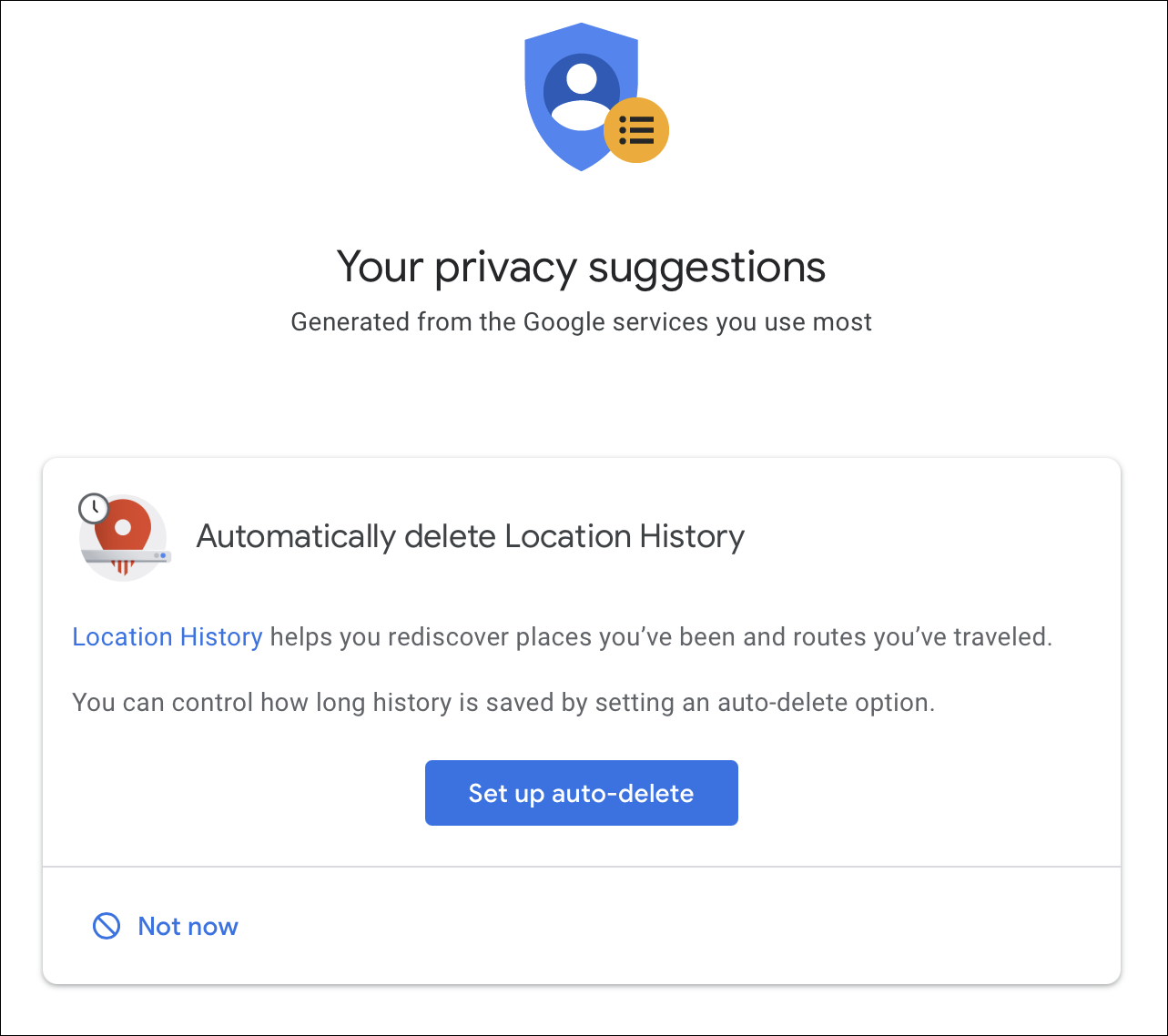
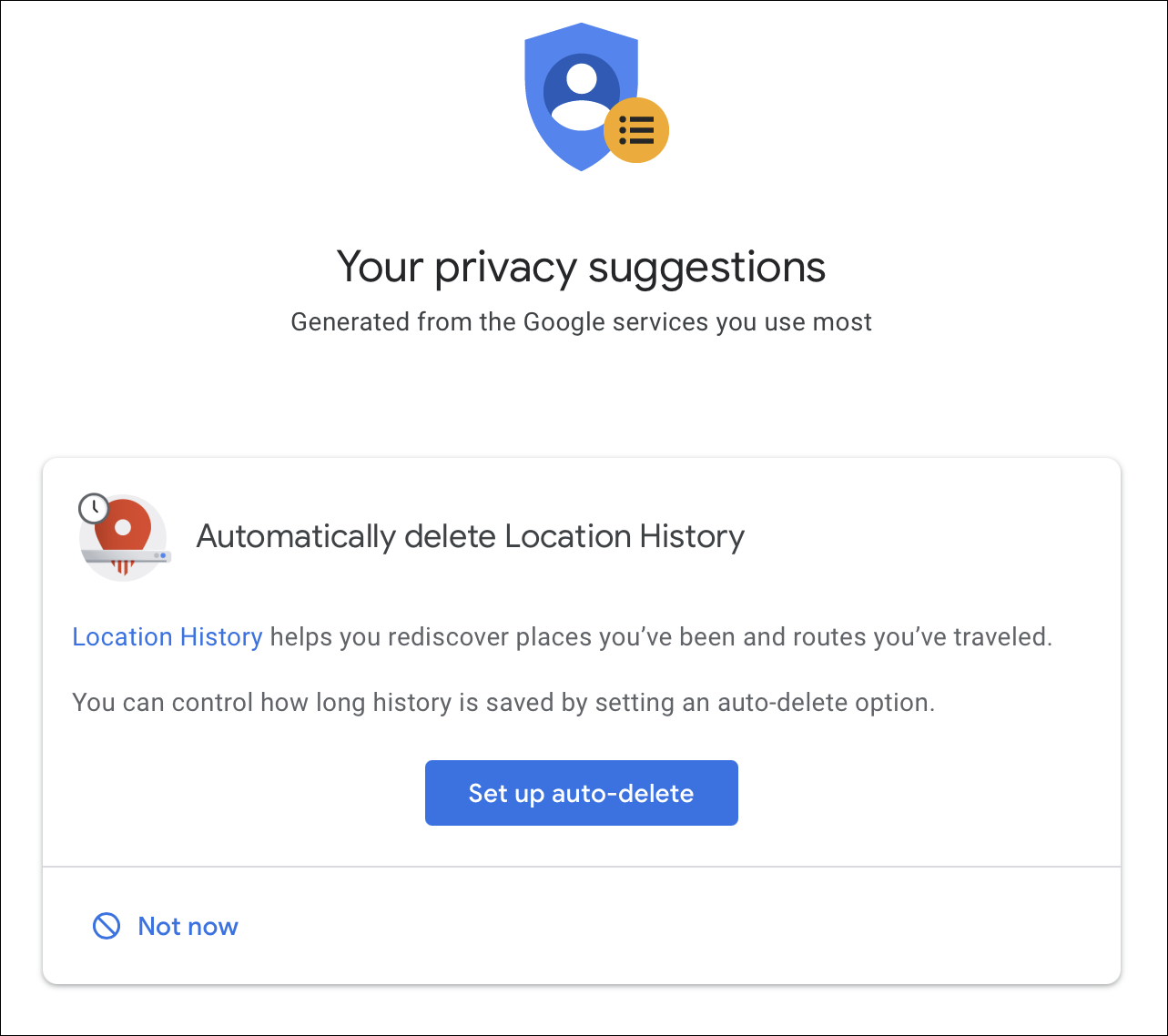
This section offers a number of options. You can Take the Privacy Checkup, which walks you through a number of settings about how much of your data is stored and/or shared. This covers your “Google experience,” YouTube, Google Photos, information that others can see, and ad preferences.
One option available here is to enable auto-deletion of your location history, which you may want to do if you use Google Maps.
In the Personalize your Google experience section, you can turn on or off the recording of certain types of information such as Web & App Activity, Location History, Device Information, Voice & Audio activity, and YouTube Watch History. You can then manage what you share on YouTube, control what others see about you, and more.
Security
In the Security section, you’ll see some settings that also show up in the Google Security Checkup, described above. But there is also a Signing in to other sites section, which lists any websites where you gave signed in with your Google account. It’s a good idea to check these. The Password Manager section lists passwords that you have stored in Google Chrome; these are independent of any third-party password manager you may use. And Linked Accounts are ones where you have given Google access to your data from third-party sites. Check those, if there are any.
People & sharing
This section gives you access to your contacts, if you are using an Android device or Chromebook, and also lets you manage location sharing and lets you choose what others see about you (which are also available in the Personalize your Google experience section discussed above).
Payments & subscriptions
This section covers payment information, purchases, subscriptions, and reservations that you have paid for with Google Pay. If you don’t use Google Pay, you won’t have any data here. However, I found that I had an old, expired credit card in the Payment methods section; I don’t remember ever using it, and it had expired two years ago, but I deleted it anyway.
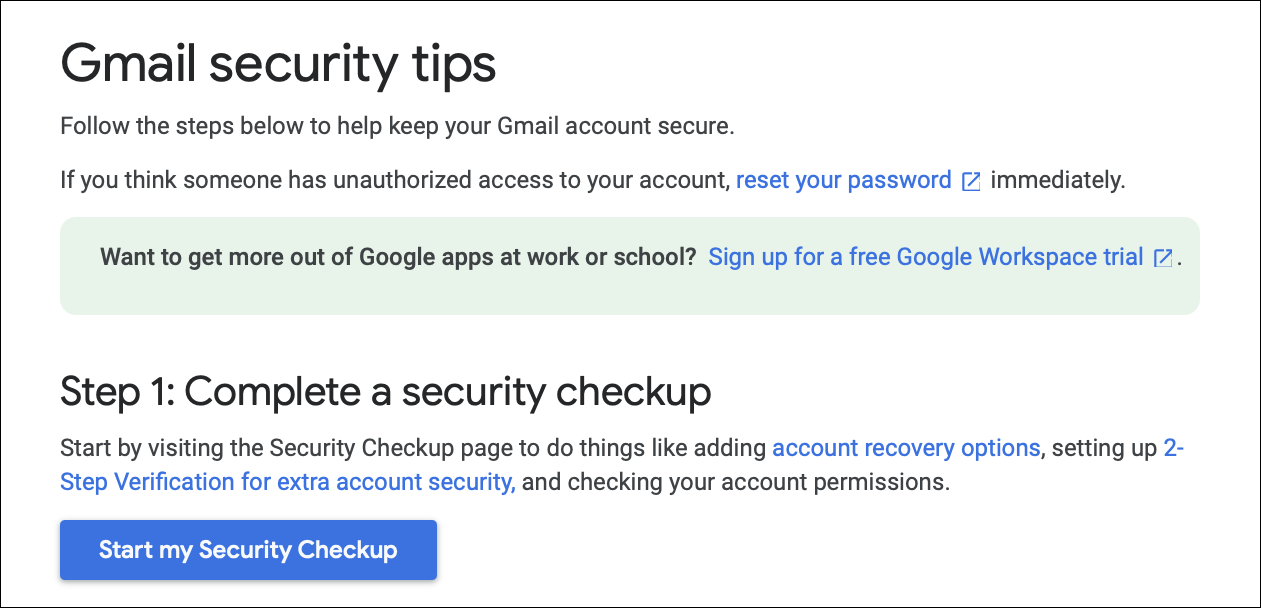
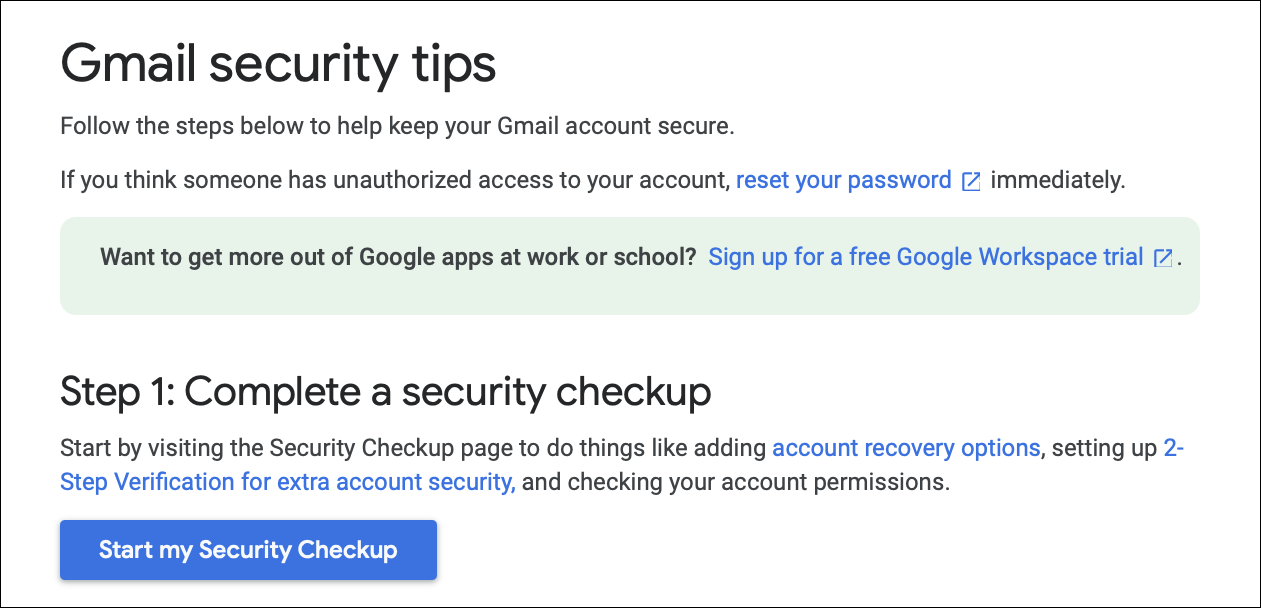
Gmail security tips
The Gmail Security tips page gives you some advice on securing your Gmail account. The first step sends you to the Google Security Checkup discussed above. The second step is a number of security tips specific to a computer, an Android device, or an iPhone or iPad. It includes items such as creating a strong password, checking your Gmail settings (see below), updating your browser, and reporting scams, spam, and phishing.
Gmail settings
To check settings for your Gmail account, log into that account. Above your inbox, to the right, you’ll see a gear icon. Click this, then click See all Settings. This page has a number of tabs, and dozens of individual settings. Most of these affect the way Gmail displays, how it handles different types of messages, any filtered or blocked addresses, and more. If you go to the Accounts tab, then the Google Account Settings, this takes you back to the main page where we started this article.
It’s a good idea to go through all of these security and privacy checks from time to time. Even if you only use Gmail, you still need to check your overall Google account settings to make sure your data is secure and your identity is protected. Google makes it fairly easy to manage security on your account, as long as you know where to look, but they also change the layout and scope of the settings from time to time, so if you haven’t checked them in a while, this would be a good time to do so.

About Kirk McElhearn
Kirk McElhearn writes about Macs, iPods, iTunes, books, music and more on his blog Kirkville.
He is co-host of the Intego Mac Podcast and PhotoActive, and a regular contributor to The Mac Security Blog, TidBITS, and several other websites and publications.
Kirk has written more than twenty books, including Take Control books about iTunes, LaunchBar, and Scrivener.
Follow him on Twitter at @mcelhearn.
View all posts by Kirk McElhearn →
Read More
The post How to Manage Gmail and Google Security and Privacy Settings appeared first on Malware Devil.
https://malwaredevil.com/2021/03/11/how-to-manage-gmail-and-google-security-and-privacy-settings/?utm_source=rss&utm_medium=rss&utm_campaign=how-to-manage-gmail-and-google-security-and-privacy-settings