
The post Test Post appeared first on Security Boulevard.
The post Test Post appeared first on Malware Devil.
https://malwaredevil.com/2021/03/12/test-post-2/?utm_source=rss&utm_medium=rss&utm_campaign=test-post-2
Cyber Security, Network Security, Threat Intelligence, Threat Hunting, and Malware Analysis News, Tools, and Reviews.

The post Test Post appeared first on Security Boulevard.
The post Test Post appeared first on Malware Devil.

Get our best 7 data protection tips in a new infographic and a new ebook on mitigating third party & supply chain risk, plus fresh cybercrime stats!
The post Don’t Let Data-Stealing Leprechauns Snatch Your Pot of Gold appeared first on Security Boulevard.
The post Don’t Let Data-Stealing Leprechauns Snatch Your Pot of Gold appeared first on Malware Devil.

This week Dr. Doug talks Studmaster, McAfee, z0Miner, Exchange, Linux, and bad cameras! All this, with his Favorite Threat of the Week, and the show Wrap Ups for the week!
Visit https://www.securityweekly.com/swn for all the latest episodes!
Show Notes: https://securityweekly.com/swn106
The post “Studmaster”, John McAfee, Exchange Escalation, z0Miner, & Bad Cameras – Wrap Up – SWN #106 appeared first on Malware Devil.

The post 2021-03-12 – TA551 (Shathak) Italian template Word docs push Ursnif/Gozi/ISFB appeared first on Malware Devil.

The post 2021-03-12 – Quick post: IcedID malware/artifacts appeared first on Malware Devil.

 BETA
BETA 
This project is in the beta phase, we will be constantly updating the main branch, if you have found any bugs or issues, please let us know via GitHub Issues and we will try our best to get it resolved quickly.
More: https://github.com/0dayCTF/reverse-shell-generator
This is an Online Reverse Shell Generator that allows anyone to configure their IP Addresses, Ports, and Shell of choice for your favorite reverse shell payloads, this generator has functionality to save all settings in local storage, so that you can return to the site at any time and not lose any of your settings. All interactions and shells generated, never interact with the server, so no logs are created. This can also be used in real-life Penetration Tests and/or CTFs. All the shells are compiled from publicly available, and well-known one-liners. The team is constantly updating, so make sure to Bookmark the website.

gitclone https://github.com/0dayCTF/reverse-shell-generator
We are constantly working on adding new solutions for the best one-liners and listeners please feel free to suggest a new feature in our issues section https://github.com/0dayCTF/reverse-shell-generator/issues.
Thank you for the awesome, support, development, and ideas.
@weibell
I am Ryan Montgomery “0day”. My social media is https://instagram.com/0day / https://twitter.com/0dayCTF / https://facebook.com/RyanMMontgomery
The post Reverse Shell Generator by Ryan Montgomery appeared first on Hakin9 – IT Security Magazine.
The post Reverse Shell Generator by Ryan Montgomery appeared first on Malware Devil.

Hackers were able to gain access to camera feeds from Verkada, a tech company that specializes in video security and physical access control, to demonstrate how prevalent surveillance is, reports say.
Unfortunately, it also exposed the inner workings of hospitals, clinics, and mental health institutions; banks; police departments; prisons; schools; and companies like Tesla and Cloudflare, after at least 150,000 cameras were compromised as part of this demonstration.
Verkada is still investigating the scale and scope of the breach.
Swiss hacker and member of the hacking collective “APT-69420 Arson Cats,” Tillie Kottmann, claimed credit for the Verkada hack. When asked why, they told Bloomberg: “lots of curiosity, fighting for freedom of information and against intellectual property, a huge dose of anti-capitalism, a hint of anarchism—and it’s also just too much fun not to do it.”
Kottmann was also credited for breaching Intel in August 2020 and Nissan Motors in January 2021.
All of Kottmann’s tweets related to the Verkada hack contain the #OperationPanopticon hashtag, which references the panopticon, a prison architecture that allows a supervisor to have full view of its inmates without them knowing that they’re being watched. It is also a metaphor used to illustrate surveillance technology.
It isn’t clear if this operation is a name for just the Verkada hack, or a name for a series of breaches against surveillance companies that could affect millions, with Verkada just the first company to be targeted and breached.
Speaking to Bloomberg, Kottmann said this incident “exposes just how broadly we’re being surveilled, and how little care is put into at least securing the platforms used to do so, pursuing nothing but profit. It’s just wild how I can just see the things we always knew are happening, but we never got to see.”
Twitter suspended Kottmann’s account after they leaked Tesla security footage.
When asked how they were able to breach Verkada, Kottmann claimed that they were able to get an administrator account credential, which was publicly available online for some reason, with “super admin” rights, which gave them access to any camera, belonging to any of the company’s clients.
IPVM reports that a source “with direct knowledge” discovered that “basically every team member” at Verkada, including executives, had super-admin privileges.
the source with direct knowledge told @ipvideo that Verkada’s Product and Engineering teams, along with executives, had Super Admin privileges.
“The purpose was to be able to debug issues. But customers didn’t know and it was known at the company not to tell customers that.”
— Charles Rollet (@CharlesRollet1) March 10, 2021
IPVM also reports that super-admin access went further than simply letting the hackers see whatever they wanted:
Not only did Super Admin provide access to video feeds … it provided access to the root shell inside the cameras running inside each customer’s facility.
In a statement about the incident, Verkada confirmed IPVM’s reporting, admitting that attackers had “gained access to a tool that allowed the execution of shell commands on a subset of customer cameras”.
According to the company, attackers gained access via a Jenkins server “used by our support team to perform bulk maintenance operations on customer cameras”, which gave them access to “video and image data from a limited number of cameras from a subset of client organizations”. Attackers also gained access to lists of client account administrators and sales orders.
Seeking to reassure customers, the company said it had now secured its systems.
First, we have identified the attack vector used in this incident, and we are confident that all customer systems were secured as of approximately noon PST on March 9, 2021. If you are a Verkada customer, no action is required on your part.
This isn’t Verkada’s first bout with negative publicity. In October 2020, three employees were fired after they abused Verkada’s own video surveillance system to capture and pass on media of female colleagues with sexually explicit jokes in one of the company’s Slack rooms.
Motherboard’s Vice was able to interview a Verkada employee who was unimpressed by the whole incident, saying “the big picture for me having worked at the company is that it has opened my eyes to how surveillance can be abused by people in power.”
The hack raises serious questions about who had access to what, and why, and highlights both the security and privacy risks that come with admin and super-admin accounts. Simply, the more administrators there are, the more targets there are.
Administrator or super-administrator accounts should only be issued to people who need them to do their job, and those people should only use them if an account with lower privileges can’t be used. They should never be used for convenience.
Speaking to Bloomberg about the consent and privacy implications, Eva Galperin, the Electronic Frontier Foundation’s director of cybersecurity, made the point that companies who use a network of cameras may not expect that someone other than the company’s security team are watching them.
“There are many legitimate reasons to have surveillance inside of a company,” Galperin said in a Bloomberg interview. “The most important part is to have the informed consent of your employees.”
Finally, it should not be forgotten that Verkada and its customers were the victims of a crime. Accessing other people’s computers without their consent is still illegal, no matter how good your point is.
The post 150,000 Verkada security cameras hacked—to make a point appeared first on Malwarebytes Labs.
The post 150,000 Verkada security cameras hacked—to make a point appeared first on Malware Devil.

Hackers were able to gain access to camera feeds from Verkada, a tech company that specializes in video security and physical access control, to demonstrate how prevalent surveillance is, reports say.
Unfortunately, it also exposed the inner workings of hospitals, clinics, and mental health institutions; banks; police departments; prisons; schools; and companies like Tesla and Cloudflare, after at least 150,000 cameras were compromised as part of this demonstration.
Verkada is still investigating the scale and scope of the breach.
Swiss hacker and member of the hacking collective “APT-69420 Arson Cats,” Tillie Kottmann, claimed credit for the Verkada hack. When asked why, they told Bloomberg: “lots of curiosity, fighting for freedom of information and against intellectual property, a huge dose of anti-capitalism, a hint of anarchism–and it’s also just too much fun not to do it.”
Kottmann was also credited for breaching Intel in August 2020 and Nissan Motors in January 2021.
All of Kottmann’s tweets related to the Verkada hack contain the #OperationPanopticon hashtag, which references the panopticon, a prison architecture that allows a supervisor to have full view of its inmates without them knowing that they’re being watched. It is also a metaphor used to illustrate surveillance technology.
It isn’t clear if this operation is a name for just the Verkada hack, or a name for a series of breaches against surveillance companies that could affect millions, with Verkada just the first company to be targeted and breached.
Speaking to Bloomberg, Kottmann said this incident “exposes just how broadly we’re being surveilled, and how little care is put into at least securing the platforms used to do so, pursuing nothing but profit. It’s just wild how I can just see the things we always knew are happening, but we never got to see.”
Twitter suspended Kottmann’s account after they leaked Tesla security footage.
When asked how they were able to breach Verkada, Kottmann claimed that they were able to get an administrator account credential, which was publicly available online for some reason, with “super admin” rights, which gave them access to any camera, belonging to any of the company’s clients.
IPVM reports that a source “with direct knowledge” discovered that “basically every team member” at Verkada, including executives, had super-admin privileges.
the source with direct knowledge told @ipvideo that Verkada’s Product and Engineering teams, along with executives, had Super Admin privileges.
“The purpose was to be able to debug issues. But customers didn’t know and it was known at the company not to tell customers that.”
— Charles Rollet (@CharlesRollet1)
IPVM also reports that super-admin access went further than simply letting the hackers see whatever they wanted:
Not only did Super Admin provide access to video feeds … it provided access to the root shell inside the cameras running inside each customer’s facility.
In a statement about the incident, Verkada confirmed IPVM’s reporting, admitting that attackers had “gained access to a tool that allowed the execution of shell commands on a subset of customer cameras”.
According to the company, attackers gained access via a Jenkins server “used by our support team to perform bulk maintenance operations on customer cameras”, which gave them access to “video and image data from a limited number of cameras from a subset of client organizations”. Attackers also gained access to lists of client account administrators and sales orders.
Seeking to reassure customers, the company said it had now secured its systems.
First, we have identified the attack vector used in this incident, and we are confident that all customer systems were secured as of approximately noon PST on March 9, 2021. If you are a Verkada customer, no action is required on your part.
This isn’t Verkada’s first bout with negative publicity. In October 2020, three employees were fired after they abused Verkada’s own video surveillance system to capture and pass on media of female colleagues with sexually explicit jokes in one of the company’s Slack rooms.
Motherboard’s Vice was able to interview a Verkada employee who was unimpressed by the whole incident, saying “the big picture for me having worked at the company is that it has opened my eyes to how surveillance can be abused by people in power.”
The hack raises serious questions about who had access to what, and why, and highlights both the security and privacy risks that come with admin and super-admin accounts. Simply, the more administrators there are, the more targets there are.
Administrator or super-administrator accounts should only be issued to people who need them to do their job, and those people should only use them if an account with lower privileges can’t be used. They should never be used for convenience.
Speaking to Bloomberg about the consent and privacy implications, Eva Galperin, the Electronic Frontier Foundation’s director of cybersecurity, made the point that companies who use a network of cameras may not expect that someone other than the company’s security team are watching them.
“There are many legitimate reasons to have surveillance inside of a company,” Galperin said in a Bloomberg interview. “The most important part is to have the informed consent of your employees.”
Finally, it should not be forgotten that Verkada and its customers were the victims of a crime. Accessing other people’s computers without their consent is still illegal, no matter how good your point is.
The post 150,000 Verkada security cameras hacked–to make a point appeared first on Malware Devil.

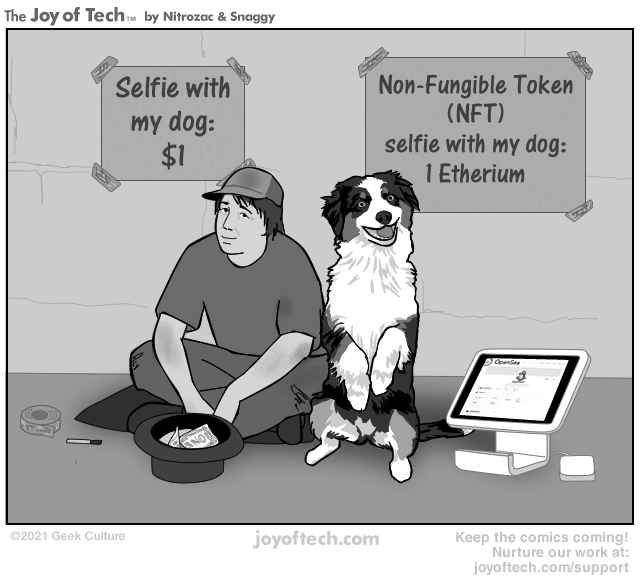
via the Comic Noggins of Nitrozac and Snaggy at The Joy of Tech®!
The post Joy Of Tech® ‘NFT Entrepreneur’ appeared first on Security Boulevard.
The post Joy Of Tech® ‘NFT Entrepreneur’ appeared first on Malware Devil.

The post Microsoft Exchange Vulnerabilities – After Action Review and Outlook appeared first on Fidelis Cybersecurity.
The post Microsoft Exchange Vulnerabilities – After Action Review and Outlook appeared first on Security Boulevard.
The post Microsoft Exchange Vulnerabilities – After Action Review and Outlook appeared first on Malware Devil.

-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA256
===========================================================================
AUSCERT External Security Bulletin Redistribution
ESB-2021.0883
Red Hat Integration Tech-Preview 3 Camel K security update
12 March 2021
===========================================================================
AusCERT Security Bulletin Summary
---------------------------------
Product: Red Hat Integration Tech-Preview 3 Camel K
Publisher: Red Hat
Operating System: Red Hat
Impact/Access: Access Confidential Data -- Remote/Unauthenticated
Reduced Security -- Remote/Unauthenticated
Resolution: Patch/Upgrade
CVE Names: CVE-2020-25649 CVE-2020-13956 CVE-2020-13946
Reference: ESB-2021.0598
ESB-2021.0379
Original Bulletin:
https://access.redhat.com/errata/RHSA-2021:0811
- --------------------------BEGIN INCLUDED TEXT--------------------
- -----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA256
=====================================================================
Red Hat Security Advisory
Synopsis: Low: Red Hat Integration Tech-Preview 3 Camel K security update
Advisory ID: RHSA-2021:0811-01
Product: Red Hat Integration
Advisory URL: https://access.redhat.com/errata/RHSA-2021:0811
Issue date: 2021-03-11
Keywords: fuse
CVE Names: CVE-2020-13946 CVE-2020-13956 CVE-2020-25649
=====================================================================
1. Summary:
An update to the Camel K operator image for Red Hat Integration
tech-preview is now available. The purpose of this text-only errata is to
inform you about the security issues fixed in this release.
Red Hat Product Security has rated this update as having a security impact
of Low. A Common Vulnerability Scoring System (CVSS) base score, which
gives a detailed severity rating, is available for each vulnerability from
the CVE link(s) in the References section.
2. Description:
This release of Red Hat Integration - Camel K - Tech-Preview 3 serves as a
replacement for tech-preview 2, and includes bug fixes and enhancements,
which are documented in the Release Notes document linked to in the
References.
Security Fix(es):
* jackson-databind: FasterXML DOMDeserializer insecure entity expansion is
vulnerable to XML external entity (XXE) (CVE-2020-25649)
* cassandra: allows manipulation of the RMI registry to perform a MITM
attack and capture user names and passwords used to access the JMX
interface (CVE-2020-13946)
* apache-httpclient: incorrect handling of malformed authority component in
request URIs (CVE-2020-13956)
For more details about the security issue(s), including the impact, a CVSS
score, acknowledgments, and other related information, refer to the CVE
page(s) listed in the References section.
3. Solution:
For details on how to apply this update, which includes the changes
described in this advisory, refer to:
https://access.redhat.com/articles/11258
4. Bugs fixed (https://bugzilla.redhat.com/):
1875830 - CVE-2020-13946 cassandra: allows manipulation of the RMI registry to perform a MITM attack and capture user names and passwords used to access the JMX interface
1886587 - CVE-2020-13956 apache-httpclient: incorrect handling of malformed authority component in request URIs
1887664 - CVE-2020-25649 jackson-databind: FasterXML DOMDeserializer insecure entity expansion is vulnerable to XML external entity (XXE)
5. References:
https://access.redhat.com/security/cve/CVE-2020-13946
https://access.redhat.com/security/cve/CVE-2020-13956
https://access.redhat.com/security/cve/CVE-2020-25649
https://access.redhat.com/security/updates/classification/#low
https://access.redhat.com/documentation/en-us/red_hat_integration/2021.q1/html-single/release_notes_for_red_hat_integration_2021.q1
6. Contact:
The Red Hat security contact is . More contact
details at https://access.redhat.com/security/team/contact/
Copyright 2021 Red Hat, Inc.
- -----BEGIN PGP SIGNATURE-----
Version: GnuPG v1
iQIVAwUBYEpYr9zjgjWX9erEAQg+tg/+JACoMEuY7tXs0SZd8SFeLgg4h9Zz2txG
IqQ+IamXNHsEITUntC2aux58wz0T7LajDIfUZvrlYtyBPYOC+0ej3f7k7DDu6xYM
62txbRYGeWYCQmgJKzZEcz1aaSuEBg0+elJyMz0WpMXuDHwOXsu0O6sITT1Q14mj
vMqsQCH+NgGLOjbqGrk9Y1EolfmgJ/pL1d3011Bm1/fJ1n0yXwj/q4sxgaXc30+g
K7817SCnp7H+NP/b6HnjxpZ+MpIijtGcAXIVV/lGp7cmz0a6QP8bIY8BDA/KuAYu
oeO6jRzNfLk+RQ+qwMBFX1hUb/wRS7VDTkjO1poeFKhEBuqi6lshYl9sOaZsQ0Bd
zq4buG5/PKuqEcudv7ClbLIf8Ls3RJym6phzztpxegqBx3mZqcL9uAfgdms1gkta
d7uZdIyATkBFs1uWlvhg4TWxKwFbCSok5w19btOSXTm2ssNtQJajSnWVF6/HD2Jy
5TbSkuwCZNl3NevLn0oC04Adm/k/KoPkLE20H5d1lLT+AIh80SXcfi6GBDq3eTXU
eeWoRBYd1S1tuuB65Nl9XyJtYEvyfnxH3CQg0QOQ8G1KV7Vsdaaf/qlqPuDrrlFa
kJixFJtZoiUiEe+mEU2GSZPADMaE8rJbjEeJpNgRdvL6oIovwpQPEVRjq/alJm7X
N+BCQ4ggO/E=
=ERpK
- -----END PGP SIGNATURE-----
- --------------------------END INCLUDED TEXT--------------------
You have received this e-mail bulletin as a result of your organisation's
registration with AusCERT. The mailing list you are subscribed to is
maintained within your organisation, so if you do not wish to continue
receiving these bulletins you should contact your local IT manager. If
you do not know who that is, please send an email to auscert@auscert.org.au
and we will forward your request to the appropriate person.
NOTE: Third Party Rights
This security bulletin is provided as a service to AusCERT's members. As
AusCERT did not write the document quoted above, AusCERT has had no control
over its content. The decision to follow or act on information or advice
contained in this security bulletin is the responsibility of each user or
organisation, and should be considered in accordance with your organisation's
site policies and procedures. AusCERT takes no responsibility for consequences
which may arise from following or acting on information or advice contained in
this security bulletin.
NOTE: This is only the original release of the security bulletin. It may
not be updated when updates to the original are made. If downloading at
a later date, it is recommended that the bulletin is retrieved directly
from the author's website to ensure that the information is still current.
Contact information for the authors of the original document is included
in the Security Bulletin above. If you have any questions or need further
information, please contact them directly.
Previous advisories and external security bulletins can be retrieved from:
https://www.auscert.org.au/bulletins/
===========================================================================
Australian Computer Emergency Response Team
The University of Queensland
Brisbane
Qld 4072
Internet Email: auscert@auscert.org.au
Facsimile: (07) 3365 7031
Telephone: (07) 3365 4417 (International: +61 7 3365 4417)
AusCERT personnel answer during Queensland business hours
which are GMT+10:00 (AEST).
On call after hours for member emergencies only.
===========================================================================
-----BEGIN PGP SIGNATURE-----
Comment: http://www.auscert.org.au/render.html?it=1967
iQIVAwUBYEqtxONLKJtyKPYoAQgcyhAAhatQoULM5Uv+A/JDwOtfbO2HTNqtm8hW
lZ/kVbSYOV105m9svuhNFCl0zofkY6Jsz9hqZgvyGiNVvIkI7QcVVsSSimGzg+U7
rgGiNAjlwNm83SqIP0Fon+NAqJDv2wbyMi2ouN8eyrntvCozuBGxpSdlw963qu6/
Ll9V9Ew+rnZOZab0CHrnKEowxLX65lCCAk0pdWEEjswbO/pnMUxF5ciKzff1sGH9
mjRw3raSKr6GrN8CIsBJU5u0SaB57DagfEs3PTPIdJfCcK86D3ZX10+2QbGbvdYj
QCxQJvGPkMeB2FDjN4GEuB3okKT0te7HsyN40iKZWXhaX3qo8oHycvuWmv4cB1Dt
593/GDGBwj8oI71Ly2RpZ24e+kJAdmKfvS/od5/w9kdWIWAH3G3a5fXa3VuSNwOa
+nWxJlyFM0BUMgm/lQ+aeeWrNI83sWEAdqGEC3/I2U+lW7eH+GC9xJI4n5OEotff
ZDIvUuzjGMMm7k6jqGPVP3Ec1hJ84vY3N+YFbYcQbi+WsjQ3J5YuCAAnXNQIp8mK
ljtLAW4eOxNQLBiskuVFPP2lCpJZ5+IW1UUXk+5MK7gXzR8fl0gXV5K9x+aSduqK
IUH1yF5w8cWVIXv5QFY7EmeugxOKXry2ispX6HlCQtlK9kZ69MTJ6mSLhsE3f4Mm
niJhQiEyxeU=
=bIY4
-----END PGP SIGNATURE-----
The post ESB-2021.0883 – [RedHat] Red Hat Integration Tech-Preview 3 Camel K: Multiple vulnerabilities appeared first on Malware Devil.

-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA256
===========================================================================
AUSCERT External Security Bulletin Redistribution
ESB-2021.0887
USN-4763-1: Pillow vulnerabilities
12 March 2021
===========================================================================
AusCERT Security Bulletin Summary
---------------------------------
Product: Pillow
Publisher: Ubuntu
Operating System: Ubuntu
UNIX variants (UNIX, Linux, OSX)
Windows
Impact/Access: Execute Arbitrary Code/Commands -- Remote/Unauthenticated
Denial of Service -- Remote/Unauthenticated
Resolution: Patch/Upgrade
CVE Names: CVE-2021-27923 CVE-2021-27922 CVE-2021-27921
CVE-2021-25293 CVE-2021-25292 CVE-2021-25291
CVE-2021-25290 CVE-2021-25289
Original Bulletin:
https://ubuntu.com/security/notices/USN-4763-1
Comment: This advisory references vulnerabilities in products which run on
platforms other than Ubuntu. It is recommended that administrators
running Pillow check for an updated version of the software for
their operating system.
- --------------------------BEGIN INCLUDED TEXT--------------------
USN-4763-1: Pillow vulnerabilities
11 March 2021
Several security issues were fixed in Pillow.
Releases
o Ubuntu 20.10
o Ubuntu 20.04 LTS
o Ubuntu 18.04 LTS
o Ubuntu 16.04 LTS
Packages
o pillow - Python Imaging Library
Details
It was discovered that Pillow incorrectly handled certain Tiff image files.
If a user or automated system were tricked into opening a specially-crafted
Tiff file, a remote attacker could cause Pillow to crash, resulting in a
denial of service, or possibly execute arbitrary code. This issue only
affected Ubuntu 20.04 LTS and Ubuntu 20.10. ( CVE-2021-25289 ,
CVE-2021-25291 )
It was discovered that Pillow incorrectly handled certain Tiff image files.
If a user or automated system were tricked into opening a specially-crafted
Tiff file, a remote attacker could cause Pillow to crash, resulting in a
denial of service, or possibly execute arbitrary code. ( CVE-2021-25290 )
It was discovered that Pillow incorrectly handled certain PDF files. If a
user or automated system were tricked into opening a specially-crafted
PDF file, a remote attacker could cause Pillow to hang, resulting in a
denial of service. This issue only affected Ubuntu 18.04 LTS, Ubuntu 20.04
LTS, and Ubuntu 20.10. ( CVE-2021-25292 )
It was discovered that Pillow incorrectly handled certain SGI image files.
If a user or automated system were tricked into opening a specially-crafted
SGI file, a remote attacker could possibly cause Pillow to crash,
resulting in a denial of service. This issue only affected Ubuntu 18.04
LTS, Ubuntu 20.04 LTS, and Ubuntu 20.10. ( CVE-2021-25293 )
Jiayi Lin, Luke Shaffer, Xinran Xie, and Akshay Ajayan discovered that
Pillow incorrectly handled certain BLP files. If a user or automated system
were tricked into opening a specially-crafted BLP file, a remote attacker
could possibly cause Pillow to consume resources, resulting in a denial of
service. This issue only affected Ubuntu 18.04 LTS, Ubuntu 20.04 LTS, and
Ubuntu 20.10. ( CVE-2021-27921 )
Jiayi Lin, Luke Shaffer, Xinran Xie, and Akshay Ajayan discovered that
Pillow incorrectly handled certain ICNS files. If a user or automated
system were tricked into opening a specially-crafted ICNS file, a remote
attacker could possibly cause Pillow to consume resources, resulting in a
denial of service. ( CVE-2021-27922 )
Jiayi Lin, Luke Shaffer, Xinran Xie, and Akshay Ajayan discovered that
Pillow incorrectly handled certain ICO files. If a user or automated
system were tricked into opening a specially-crafted ICO file, a remote
attacker could possibly cause Pillow to consume resources, resulting in a
denial of service. ( CVE-2021-27922 )
Update instructions
The problem can be corrected by updating your system to the following package
versions:
Ubuntu 20.10
o python3-pil - 7.2.0-1ubuntu0.2
Ubuntu 20.04
o python3-pil - 7.0.0-4ubuntu0.3
Ubuntu 18.04
o python3-pil - 5.1.0-1ubuntu0.5
o python-pil - 5.1.0-1ubuntu0.5
Ubuntu 16.04
o python3-pil - 3.1.2-0ubuntu1.6
o python-pil - 3.1.2-0ubuntu1.6
In general, a standard system update will make all the necessary changes.
References
o CVE-2021-27922
o CVE-2021-25291
o CVE-2021-27921
o CVE-2021-25293
o CVE-2021-27923
o CVE-2021-25290
o CVE-2021-25292
o CVE-2021-25289
- --------------------------END INCLUDED TEXT--------------------
You have received this e-mail bulletin as a result of your organisation's
registration with AusCERT. The mailing list you are subscribed to is
maintained within your organisation, so if you do not wish to continue
receiving these bulletins you should contact your local IT manager. If
you do not know who that is, please send an email to auscert@auscert.org.au
and we will forward your request to the appropriate person.
NOTE: Third Party Rights
This security bulletin is provided as a service to AusCERT's members. As
AusCERT did not write the document quoted above, AusCERT has had no control
over its content. The decision to follow or act on information or advice
contained in this security bulletin is the responsibility of each user or
organisation, and should be considered in accordance with your organisation's
site policies and procedures. AusCERT takes no responsibility for consequences
which may arise from following or acting on information or advice contained in
this security bulletin.
NOTE: This is only the original release of the security bulletin. It may
not be updated when updates to the original are made. If downloading at
a later date, it is recommended that the bulletin is retrieved directly
from the author's website to ensure that the information is still current.
Contact information for the authors of the original document is included
in the Security Bulletin above. If you have any questions or need further
information, please contact them directly.
Previous advisories and external security bulletins can be retrieved from:
https://www.auscert.org.au/bulletins/
===========================================================================
Australian Computer Emergency Response Team
The University of Queensland
Brisbane
Qld 4072
Internet Email: auscert@auscert.org.au
Facsimile: (07) 3365 7031
Telephone: (07) 3365 4417 (International: +61 7 3365 4417)
AusCERT personnel answer during Queensland business hours
which are GMT+10:00 (AEST).
On call after hours for member emergencies only.
===========================================================================
-----BEGIN PGP SIGNATURE-----
Comment: http://www.auscert.org.au/render.html?it=1967
iQIVAwUBYEqvJeNLKJtyKPYoAQjSkg//SAbV6eEt/sjsJjUV7fpEVCCRFMGpDsU/
id0aMORu7P+NVivkWtBNa0Phn4p7A2ylO/XOHjefOzKFb+rm7C77qSP90a4iwtsd
1Y5NhPOS0B5ZZA7HTuMUN2xrmE4jnDJVTKE45h0Lr+HXWcajbugHkLLQ4z8+ku0w
BO73D+jwgYN/jjx4spymdf7f0w2HBdQnnf4XBAae5u/7WnJ89Zx0+72TBGFkJhbo
1LvPvNdjKmHAkpKOlDuquC4zhjYc1nwLNuDoRc+NRPR7QGhXcerfRKFU7HtUp7A+
+dX6+B4E7lRNoLyne0lcs/xz+TpVH8+pTtzm3Ewvcj3d0FUuUoGJV76YLay9igH6
7N6QcdxtDE/2BwX3uIYUT2G0vHhkxqs1EHtNy/C9oW8dTrOES2FUfSWt9ZdyC9uK
vwCAR9WgSMDaz7p/KGs8Rev+VG2EOkRaI3+ABzXbj9Nrzl3l7Ex0ZHFCAomYb03W
xZVTFpL4Q8MktmqFAFmFOCwF/huRNsFAxROccQUhzjopMq4yt310PF6QPDFEgehj
8R0KH5IjPoTXX/bMnbopBXNKD/vU5+YLi+5nHKf7K7YE+GtMrH0aakIzeqqjNkAl
0nmwyzpkKLVT5zUSH5Nzjwkky8ngFCMc/KKIWnU9Rw89fP1coQS4iHAdcFr2d3oK
/PakbrCYhD0=
=DaiP
-----END PGP SIGNATURE-----
The post ESB-2021.0887 – [Win][UNIX/Linux][Ubuntu] Pillow: Multiple vulnerabilities appeared first on Malware Devil.

David has been studying the structure, size and scope of illicit markets for over 10 years. He has come to realize just how fragmented illicit markets are, how a few select vendors often control most of the sales, and how important social bonds are even in the context of anonymous illicit markets.
Visit https://www.securityweekly.com/psw for all the latest episodes!
Show Notes: https://securityweekly.com/psw686
The post How Illicit Markets Really Operate – David Hétu – PSW #686 appeared first on Malware Devil.

A brief daily summary of what is important in cybersecurity. The podcast is published every weekday and designed to get you ready for the day with a brief, usually about 5 minutes long, summary of current network security-related events. The content is late breaking, educational and based on listener input as well as on input received by the SANS Internet Storm Center. You may submit questions and comments via our contact form at https://isc.sans.edu/contact.html .
The post Network Security News Summary for Friday March 12nd, 2021 appeared first on Malware Devil.

Enterprise organizations using F5 Networks’ BIG-IP and BIG-IQ application delivery technologies are being urged to immediately update their systems to address multiple critical vulnerabilities in the products.
Several of the vulnerabilities enable remote attackers to take complete control of the systems to execute malicious code, disable services, create or delete files, and take other malicious actions.
“Unlike previous notable F5 exploits, not all of these can be easily hand-waved away by restricting external access to the administrative interfaces known as the ‘control plane,'” says Justin Rhinehart, senior analyst at Bishop Fox. Two critical exploits disclosed this week affect the so-called data plane, which is the part responsible for handing any and all traffic going through the BIG-IP platform, he says. The only way to mitigate these exploits is by patching.
In a worst-case scenario, Rhinehart says, an attacker can use a vulnerable F5 BIG-IP appliance to break into the broader enterprise network.
“Remote command execution in a location with such privileged access is absolutely the stuff of nightmares,” he says, “Attackers can use these devices to gain a foothold on a victim’s network [and] attack sensitive targets that are not usually accessible from the outside world.”
F5 Networks on Wednesday disclosed four critical vulnerabilities in BIG-IP 11.6 or 12.x and newer — one of which also impacted versions 6.x and 7.x of the company’s BIG-IQ centralized management technology. In addition, F5 announced seven high severity bugs and 10 medium security issues impacting BIG-IP and BIG-IQ — technologies that many enterprise organizations use for a range of application delivery services, such as access control, load balancing, and app security. The company has released patches for all disclosed issues.
In a blog, F5 networks describes the vulnerabilities as impacting all BIG-IP and BIG-IQ customers and instances. The vendor urges customers to update their installations of these technologies to the fixed versions as quickly as possible. It was a sentiment echoed by the Department of Homeland Security’s Cybersecurity and Information Security Agency (CISA) in an advisory Wednesday.
“CISA encourages users and administrators review the F5 advisory and install updated software as soon as possible,” the agency said.
Last June, CISA warned that F5 Networks’ BIG-IP technology presented a big target for attackers because of the access these devices provide to enterprise networks. At that time, the agency was responding to reports about attackers actively exploiting another critical vulnerability in BIG-IP that, like the latest batch of bugs, allowed for complete system compromise.
Critical Impact
The four critical vulnerabilities that F5 Networks announced this week are an unauthenticated remote command execution (RCE) vulnerability in BIG-IP iControl REST interface (CVE-2021-22986); a similar RCE vulnerability in the Traffic Management User Interface (CVE-2021-22987); a buffer-overflow bug in the technology’s Traffic Management Microkernel (CVE-2021-22991); and an advanced WAF/ASM buffer-overflow vulnerability (CVE-2021-22992).
All four of the critical flaws have a severity rating of 9 or more, indicating they are considered as highly critical. Two of the bugs allow remote attackers to execute arbitrary system commands and to delete or create files and disable critical service. One of flaws (CVE-2021-22987) gives attackers a way to trigger a total system compromise, and the fourth (CVE-2021-22992) enables attackers to execute denial-of-service attacks.
Rhinehart says vulnerabilities are critical because the BIG-IP platform is meant to control all data entering and exiting a network.
“Unauthenticated remote code execution against any application is scary enough, but their importance, location in the network, and prevalence [of BIG-IP] really takes this one to the next level,” he says.
For organizations with the impacted technologies, the RCE flaw in the iControl REST Interface likely poses the biggest immediate threat because of the relative ease with which it can be exploited, Rhinehart says.
“In the weeks and months to come, the two vulnerabilities affecting the data plane [CVE-2021-22991 and CVE-2021-22992] become more and more of a concern as people dig deeper into how they work and write advanced exploits that may allow for remote code executions,” he explains.
Companies that cannot immediately update to the latest patched versions F5 announced this week should disable access to the iControl REST interface, though this can be tricky, Rhinehart adds. He recommends organizations that are unsure about how to do this should refer to F5 Networks’ guidance on the topic.
Jai Vijayan is a seasoned technology reporter with over 20 years of experience in IT trade journalism. He was most recently a Senior Editor at Computerworld, where he covered information security and data privacy issues for the publication. Over the course of his 20-year … View Full Bio
Recommended Reading:
Comment |
Print |
More Insights
The post F5 Networks Urges Customers to Update to New Versions of Its App Delivery Tech appeared first on Malware Devil.

F5 BIG-IP and BIG-IQ have multiple critical vulnerabilities that enable attackers to completely compromise systems.
The post F5 Networks Urges Customers to Update to New Versions of Its App Delivery Tech appeared first on Malware Devil.

In 2020, security teams had to endure a great deal of chaos — not just from the events caused by the pandemic, but by a significant series of changes in the vulnerability landscape, according to Rapid7.
In its “2020 Vulnerability Intelligence Report,” released today, the security firm documented 50 vulnerabilities representing shifts that defenders had to contend with. Fourteen vulnerabilities were exploited by nation-state actors and cybercriminals in indiscriminate campaigns that impacted a wide variety of organizations, 16 vulnerabilities were used in targeted attacks by sophisticated actors, and 20 flaws have not yet been seen in the wild but are expected to be used by attackers in their campaigns.
The company delves into the threats to offer defenders a better understanding of what constituted dangerous vulnerabilities in 2020, says Caitlin Condon, manager of software engineering at Rapid7.
“There was a pervasive feeling in the information-security community, especially among defenders, that the sky was falling nearly all the time,” she says. “It is often very difficult for the people in charge of security to look at all the research materials and all the artifacts — at all the information about a vulnerability — and determine why a vulnerability may matter or not matter for their risk model.”
In the report, Rapid7 breaks down the threats into flaws exploited indiscriminately in widespread attacks (28%), security issues — often, zero-day vulnerabilities — used in targeted attacks (32%), and vulnerabilities the company considers to be impending threats (40%).
Among the most serious threats were attacks on network and security appliances that allowed the attacker to pivot from outside the network to the internal network. So-called network pivots were discovered in Citrix NetScaler, SonicWall SonicOS, Palo Alto Networks PAN-OS, and the Sophos XG Firewall.
“For many network defenders, June 29 through July 29, 2020 was a particularly nightmarish stretch of an already challenging year: No fewer than four CVSS 10 vulnerabilities hit advisories, mailing lists, and news alerts during this period, three of which occurred within two weeks of one another,” Rapid7 states in the report. “In each of these cases, the gateway position of the vulnerable products amplified the vulnerabilities’ severity and deepened the impact of exploitation.”
Patch bypasses also became a major issue in 2020, which was — according to Rapid7’s report — “a banner year.” While companies have typically come to trust software vendors to create security updates that not only fix the original issue but also related issues, a number of notably problematic patches were published in 2020. The company details nine vulnerabilities that either had an incomplete patch that attackers were able to evade or that allowed attackers to use a similar or related issue to bypass the patch.
“In some cases, a vulnerability’s complexity can make solutions correspondingly complex to develop quickly and well,” the company states in the report.
This matches with previous research released in February, where Google’s Project Zero team found nine of the 24 zero-day vulnerabilities detected in 2020 were variants of previously patched issues. While companies expect patches to fix a family of vulnerabilities, attackers look at patches as a source of intelligence, Rapid7 states.
“Attackers work off a wholly different guiding principle — namely, that the discovery of one flaw means there are likely more just waiting in the wings, frequently in the same function, protocol, or section of the target product’s code base,” the company says. “However, it hardly makes sense for attackers to put effort into hunting for zero-day vulnerabilities when they can change a single character in an exploit for a patched vulnerability and blow past the patch as if it weren’t even there.”
Companies have to assess vulnerabilities within the scope of their own infrastructure to determine their risk profile, the report states. One lesson that security teams should take to heart: Those high-profile issues covered in the media are not always the most dangerous flaws, says Condon.
“Not every vulnerability that got talked about a lot in 2020 was an actual threat,” she says. “There were a bunch of vulnerabilities that perhaps slipped under the radar that were truer impending threats, so it is important for organizations to understand where their critical components are.”
Case in point: Vulnerabilities in operational technology (OT) often garnered a great deal of digital ink, but a variety of factors often reduced the actual threat to organizations. For example, one of the “more severe Ripple20” vulnerabilities was found to be nonexploitable, while the serious Amnesia:33 vulnerabilities could only be exploited in a very narrow set of circumstances.
“Whenever there are new vulnerabilities in shared libraries, the level of exploitability varies from device to device; as you might imagine, this creates quite a lot of confusion and adds another layer of complexity to the already complex industrial vulnerabilities space,” Rapid7 stated. “[M]anaging risk is difficult if not impossible without an understanding of attack surface area introduced by OT devices.”
Veteran technology journalist of more than 20 years. Former research engineer. Written for more than two dozen publications, including CNET News.com, Dark Reading, MIT’s Technology Review, Popular Science, and Wired News. Five awards for journalism, including Best Deadline … View Full Bio
Recommended Reading:
Comment |
Print |
More Insights
The post Network Pivots, Patch Bypasses: Exploits Hit Hard in 2020 appeared first on Malware Devil.

An analysis of 50 vulnerabilities finds a spectrum of risk, from widespread vulnerabilities exploited by a variety of attackers to serious issues that will likely be exploited in 2021.
The post Network Pivots, Patch Bypasses: Exploits Hit Hard in 2020 appeared first on Malware Devil.

No details yet disclosed on the cyberattack.
The post Molson Coors Beer Operations Halted by Hack appeared first on Malware Devil.

White Papers
Video
Current Issue
 2021 Top Enterprise IT TrendsWe’ve identified the key trends that are poised to impact the IT landscape in 2021. Find out why they’re important and how they will affect you today!
2021 Top Enterprise IT TrendsWe’ve identified the key trends that are poised to impact the IT landscape in 2021. Find out why they’re important and how they will affect you today!Flash Poll
Twitter Feed

Bug Report
The food-and-drink-menu plugin through 2.2.0 for WordPress allows remote attackers to execute arbitrary code because of an unserialize operation on the fdm_cart cookie in load_cart_from_cookie in includes/class-cart-manager.php.
CVE-2020-14988
PUBLISHED: 2021-03-11
An issue was discovered in Bloomreach Experience Manager (brXM) 4.1.0 through 14.2.2. It allows XSS in the login page via the loginmessage parameter, the text editor via the src attribute of HTML elements, the translations menu via the foldername parameter, the author page via the link URL, or the u…
CVE-2020-14989
PUBLISHED: 2021-03-11
An issue was discovered in Bloomreach Experience Manager (brXM) 4.1.0 through 14.2.2. It allows CSRF if the attacker uses GET where POST was intended.
CVE-2020-14987
PUBLISHED: 2021-03-11
An issue was discovered in Bloomreach Experience Manager (brXM) 4.1.0 through 14.2.2. It allows remote attackers to execute arbitrary code because there is a mishandling of the capability for administrators to write and run Groovy scripts within the updater editor. An attacker must use an AST transf…
CVE-2021-27679
PUBLISHED: 2021-03-11
Cross-site scripting (XSS) vulnerability in Navigation in Batflat CMS 1.3.6 allows remote attackers to inject arbitrary web script or HTML via the field name.
The post Molson Coors Beer Operations Halted by Hack appeared first on Malware Devil.
In 1801, the United States had a small Navy. Thomas Jefferson deployed almost half that Navy—three frigates and a schooner—to the Barbary C...

I’m the #1 hacker on the TryHackMe leaderboard https://tryhackme.com/leaderboards