On the bean-to-cup journey, dangers await around every corner. Here, well-caffeinated security experts warn the coffee industry about the threats.

(Image: Okea via Adobe Stock)
A supply chain is only as strong as its weakest link. That we know.
“But what gets less consideration is that each step in the process, every link, also has a supply chain, and all of it expands one’s attackable surface,” says Adam Levin, a cybersecurity expert and author who founded the recently acquired company Cyberscout.
Put another way, supply chain security issues spread far beyond the intended path in transporting things from Point A to Point B.
Look no further than the coveted coffee supply chain and the panic a disruption would cause all those involved – especially those who rely on that fresh cup (or two, or three … ) to kickstart and get through their days.
Relax. This is merely a hypothetical.
Just as coffee comes in many customizable variations – we all have our personal favorites – so do supply chain issues. While threats are common to many global supply chains, the coffee supply chain faces “a fundamental challenge,” says Jake Olcott, vice president of government affairs at BitSight.
“The coffee grower, manufacturer, and retailer are all individually responsible for their own security yet collectively dependent on each other and the larger system to operate efficiently and securely,” he says.
Let’s not forget the end user – the coffee drinker – who is part of the supply chain, adds Gary Golomb, chief scientist and co-founder at Awake Security.
“As I sit here drinking my Irish Coffee, it strikes me that we should clarify what part of the coffee analogy is the end user enterprise and which part is the supply chain,” he explains. “Is the coffee shop the end user enterprise? No. They are the [reseller], capable of taking [commercial off-the-shelf software] and skillfully combining them into more useful solutions, like a mocha, for instance. Therefore, it’s the coffee drinkers who are the end user enterprises, and everything that comes before them – well, us – is the supply chain.”
Spilling the Beans on Coffee Growers
So what if some truly vicious attacker came after coffee? Someone with no scruples at all, wanting to scorch the whole supply chain like a pot sitting on the burner too long?
Coffee growers would be the first ones to go.
“Most risks can be found deeper down in the supply chain – in this case, coffee growers,” says Nir Kshetri, a professor at the University of North Carolina-Greensboro, a research fellow at Kobe University, and author of four books on cybersecurity. “[Growers] are rapidly digitizing due to pressures to do so from Western retailers and other companies. However, IoT and other digital systems that coffee growers and other players in developing countries tend to use are not that safe. They use the cheapest devices, tend to use pirated software in the devices, and lack cybersecurity orientation.”
With limited funds and limited IT resources, coffee growers may be the weakest link, he says.
Roasting the Roasters
You can trust the coffee roasters, though. Or can you?
Many roasters are solidifying their security postures via transparency in their own supply chains. In fact, a group of well-known coffee roasters including Onyx Coffee Lab and Counter Culture signed a transparency pledge and openly share information such as FOB price and volume purchased, says Asser Christensen, founder of The Coffee Chronicler, a website dedicated to the world of Specialty Coffee.
“Most of these brands will also list the different components of their blends openly. So, in theory, you could purchase the same green beans and re-create the blend yourself,” he says. “Of course, this is entirely different from multinational coffee companies such as Nestle and Starbucks.”
Transparency looks to be a common approach for roasters, though it can also pose a security problem. Take, for example, a boutique coffee roaster, explains Rob McDonald, Virtru’s executive vice president of platform. That roaster likely has many commercial agreements in place, including with growers, shipping providers, its packaging manufacturer, an e-commerce platform, and regional chains of coffee and gift shops that stock its product.
“That roaster sends and receives data to and from all these partners and more, in addition to managing the payroll and operations of its small staff,” he says. “If that boutique roaster’s e-commerce platform is compromised in a way that grants access to the roaster’s other connected systems, all its data — plus the data of the aforementioned partners — is now in jeopardy. Those who have entrusted their data to the roaster, including individual consumers and enterprises alike, can suffer consequences.”
Manufacturing Coffee Mayhem
Espresso machine manufacturers haven’t got a chance. And they could take you down with them.
“Espresso machine makers are at high risk of getting roasted by ransomware,” says Ara Aslanian, a cybersecurity expert adviser to L.A Cyber Lab and CEO of Inverselogic, an IT services company.
Dan Frey, senior product manager at ExtraHop, agrees.
“Ransomware is ideal for disrupting operational technology heavily used in manufacturing and supply chain logistics,” he says. “These devices rarely contain sensitive information, and they typically don’t have high-levels of access to sensitive network resources. But if a cybercriminal can lock them down, they can functionally shutter operations until the systems are reformatted or the encryption keys are obtained, costing an organization far more than the ransom dollars requested.”
However, other concerning trends are also evolving fast.
“Another alarming concern is that the ransomware itself may only be a decoy for a larger attack,” Frey says. “If espresso machine manufacturers aren’t concerned about this yet, it’s only a matter of time.”
Unfortunately, manufacturers can also open the doors for attackers in other entities in the supply chain.
“Manufacturers make good targets for hackers because, as they build more IoT technologies into their supply chains to track components and increase efficiency, they create more vulnerabilities,” Aslanian says. “Attackers who hacked Target a few years ago got into the company’s network through its HVAC system.”
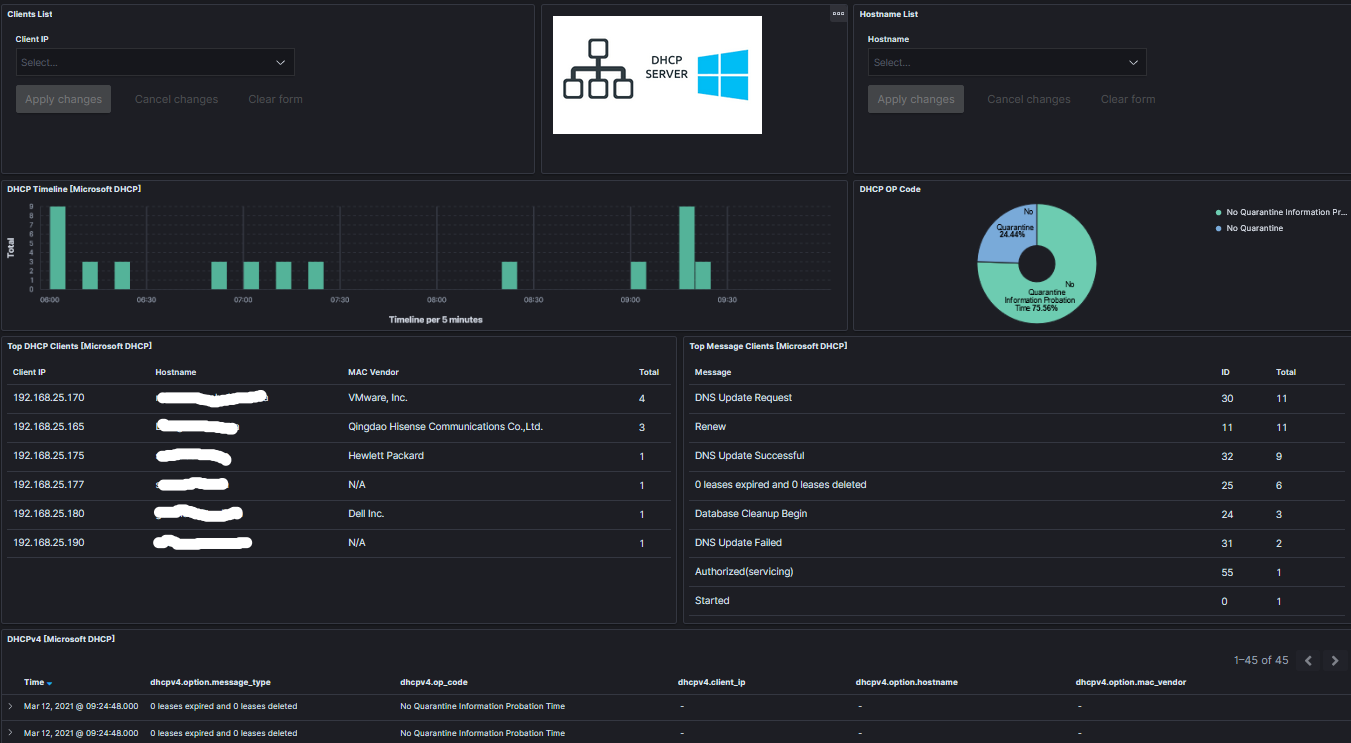
Leading smart coffee maker brands like Keurig or Braun, for example, have reason to worry about vulnerabilities built into their smart coffee makers. These popular Internet of Things (IoT) devices can brew great coffee and a pot full of trouble for some poor coffee lover at home, a company with a break room and proprietary secrets, a diner full of customer credit card payments, or the Starbucks that covers every street corner in the land.
“This is where the coffee supply chain meets the software supply chain. Any technology embedded in a device that connects to another over the internet can ultimately be exploited to gain access to network resources,” says Karen Crowley, senior product manager at ExtraHop. “For devices like smart coffee makers, where security hasn’t always been a major consideration, vulnerabilities like Ripple20, where the Treck TCP/IP stack embedded in millions of devices, could allow attackers to compromise smart devices from manufacturing to healthcare. This should serve as a wake-up call.”
These same devices also pose threats to others in the supply chain in unsuspected and unassuming ways. These same coffee makers inhabit spaces and connect to networks at manufacturers, bean growers, roasters, restaurants, and coffee shops.
“The firmware isn’t usually very sophisticated – a small chip with code written to provide certain functionalities,” says Ritesh Chaturbedi, chief operations officer at Systemax. “Due to the unsophistication and connection to the Internet and [artificial intelligence], there’s a huge risk attached. A hacker can write a code or AI to pretend as if it’s a benign Siri or Alexa and get access to the IoT device.”
The Retailers’ Brew-a-ha
Maybe your coffee makes it safely to the cup. You breathe a sigh of relief. But don’t relax yet.
(Continued on next page)
A prolific writer and analyst, Pam Baker’s published work appears in many leading publications. She’s also the author of several books, the most recent of which is “Data Divination: Big Data Strategies.” Baker is also a popular speaker at technology conferences and a member … View Full Bio

1 of 2

Recommended Reading:
Comment |
Email This |
Print |
RSS
More Insights
https://malwaredevil.com/2021/03/12/contemplating-the-coffee-supply-chain-a-horror-story/?utm_source=rss&utm_medium=rss&utm_campaign=contemplating-the-coffee-supply-chain-a-horror-story